v1g1lance.netlify.app
Crypto Key Generate Cisco 9904
- Key Generate Software
- Free Keygens Downloads
- Key Generator
- Crypto Key Generate Cisco 9904 Free
- Free Key Generate Software
- October 2, 2015
- Posted by: Syed Shujaat
- Category: Cisco, Networking Solutions
My question is will generating a crypto key using 'crypto key generate rsa mod 2048' using the cli option in asdm break anything as currently there is no crypto key. The ASAs do have VPNs configured. Because it is a live environment, I just want to ensure it will be as simple as running the command and getting ssh access to the firewalls. May 20, 2014 Author, teacher, and talk show host Robert McMillen shows you how to use the Cisco ASA version 9 generate RSA keys command. Crypto pki certificate chain TP-self-signed-##### certificate self-signed 01 (here would be numerous 8 digit Alpha-Numeric strings) quit. Just a reminder i am new to networking securities and it is alot to take in. Edit: also are these 2 commands the same? Crypto key generate rsa. Ip ssh rsa keypair-name sshkeys.
- Aug 05, 2014 crypto key generate dsa Example: RP/0/ RSP0 /CPU0:router # crypto key generate dsa Enables the SSH server for local and remote authentication on the router. The recommended minimum modulus size is 1024 bits. Generates a DSA key pair. To delete the DSA key pair, use the crypto key zeroize dsa command.
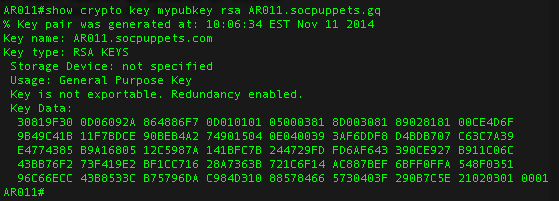
- The following is sample output from the show crypto key mypubkey rsa command. Special usage RSA keys were previously generated for this router using the crypto key generate rsa command.% Key pair was generated at: 06:07:49 UTC Jan 13 1996.
Use this command to generate RSA key pairs for your Cisco device (such as a router). keys are generated in pairs–one public RSA key and one private RSA key.
Key Generate Software
If your router already has RSA keys when you issue this command, you will be warned and prompted to replace the existing keys with new keys.
NOTE: Before issuing this command, ensure that your router has a hostname and IP domain name configured (with the hostname and ipdomain-name commands).
You will be unable to complete the cryptokeygeneratersacommand without a hostname and IP domain name. (This situation is not true when you generate only a named key pair.)
Here are the steps to Enable SSH and Crypto Key setup : 2 config must requried for SSH
1 Setup Local VTY line User ID and password
router (Config) # Line VTY 0 15
router (Config-line)# login local
To be eligible to develop Amazon MWS applications you must: Comply with the Acceptable Use Policy and Data Protection Policy. Have a Professional selling plan. For more information, see Selling plans in the Seller Central Help. Submit the Amazon MWS Developer Registration and Assessment form. We will evaluate your submission and assign you a role based on the level of Amazon MWS access you require. Feb 23, 2018 How do I get my Seller ID, AWS Access Key, and AWS Secret Access Key? How do I get my MWS API keys? Amazon Marketplace Web Service (MWS) Marketplace Web Service (Amazon MWS) Questions. Nutriheal 2013-11-06 21:32:55 UTC #1. To configure Amazon Pay, you will need your SellerID (sometimes referred to as MerchantID), Access key, and Secret key. Our User Guide provides detailed steps. To configure Login with Amazon, you will need to obtain your ClientID. Before you can develop Amazon MWS applications for yourself or others you must register as a developer on the User Permissions page in Seller Central. See Registering as a developer. To be eligible to register for Amazon MWS, you must have a Professional selling plan. The Amazon MWS keys (often referred to as the API Keys or MWS Authentication Token) are two pieces of information you will need to obtain from Amazon. These pieces of information are called the Seller ID and the MWS Auth Token. These 2 data items will be all that is required for you to authorize SellerLegend to access your Amazon account data. 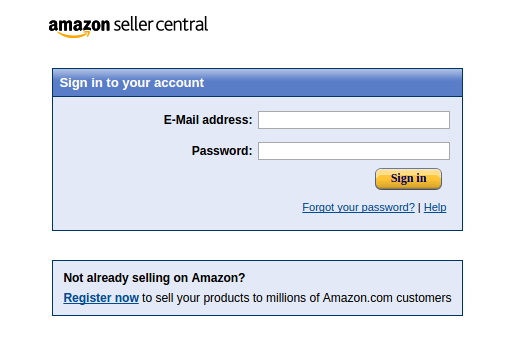
router (Config-line)# Exit
!!! create local login ID/Pass
router (Config)# username [loginid] password [cisco]
router (Config)# username loginid1 password cisco1
2. router (Config)# ip domain-name example.com
router (Config)# crypto key generate rsa
how many bits in the modulus [512] :1024
router (Config)# ip ssh version2
router (Config)# CTRL Z
Note | Secure Shell (SSH) may generate an additional RSA key pair if you generate a key pair on a router having no RSA keys. The additional key pair is used only by SSH and will have a name such as {router_FQDN }.server. For example, if a router name is “router1.cisco.com,” the key name is “router1.cisco.com.server.” |
This command is not saved in the router configuration; however, the RSA keys generated by this command are saved in the private configuration in NVRAM (which is never displayed to the user or backed up to another device) the next time the configuration is written to NVRAM.
Modulus Length
When you generate RSA keys, you will be prompted to enter a modulus length. The longer the modulus, the stronger the security. However, a longer modules take longer to generate (see the table below for sample times) and takes longer to use.
The size of Key Modulus range from 360 to 2048. Choosing modulus greater than 512 will take longer time.
| Router | 360 bits | 512 bits | 1024 bits | 2048 bits (maximum) |
|---|---|---|---|---|
| Cisco 2500 | 11 seconds | 20 seconds | 4 minutes, 38 seconds | More than 1 hour |
| Cisco 4700 | Less than 1 second | 1 second | 4 seconds | 50 seconds |
Cisco IOS software does not support a modulus greater than 4096 bits. A length of less than 512 bits is normally not recommended. In certain situations, the shorter modulus may not function properly with IKE, so we recommend using a minimum modulus of 2048 bits.
Syntax Description : Optional Strings to embed with SSH Crypto key
| general-keys | (Optional) Specifies that a general-purpose key pair will be generated, which is the default. | ||
| usage-keys | (Optional) Specifies that two RSA special-usage key pairs, one encryption pair and one signature pair, will be generated. | ||
| signature | (Optional) Specifies that the RSA public key generated will be a signature special usage key. | ||
| encryption | (Optional) Specifies that the RSA public key generated will be an encryption special usage key. | ||
| labelkey-label | (Optional) Specifies the name that is used for an RSA key pair when they are being exported.If a key label is not specified, the fully qualified domain name (FQDN) of the router is used. | ||
| exportable | (Optional) Specifies that the RSA key pair can be exported to another Cisco device, such as a router. | ||
| modulusmodulus-size | (Optional) Specifies the IP size of the key modulus.By default, the modulus of a certification authority (CA) key is 1024 bits. The recommended modulus for a CA key is 2048 bits. The range of a CA key modulus is from 350 to 4096 bits.
| ||
| storagedevicename: | (Optional) Specifies the key storage location. The name of the storage device is followed by a colon (:). | ||
| redundancy | (Optional) Specifies that the key should be synchronized to the standby CA. | ||
| ondevicename: | (Optional) Specifies that the RSA key pair will be created on the specified device, including a Universal Serial Bus (USB) token, local disk, or NVRAM. The name of the device is followed by a colon (:).Keys created on a USB token must be 2048 bits or less. |
| Command | Description |
|---|---|
| copy | Copies any file from a source to a destination, use the copy command in privileged EXEC mode. |
| cryptokeystorage | Sets the default storage location for RSA key pairs. |
| debugcryptoengine | Displays debug messages about crypto engines. |
| hostname | Specifies or modifies the hostname for the network server. |
| ipdomain-name | Defines a default domain name to complete unqualified hostnames (names without a dotted-decimal domain name). |
| showcryptokeymypubkeyrsa | Displays the RSA public keys of your router. |
| show crypto pki certificates | Displays information about your PKI certificate, certification authority, and any registration authority certificates. |
Configuration of SSH on Cisco Switch in Packet Tracer 2019
This Article is about the configuration of SSH on Cisco Switch. You can configure SSH on Cisco devices very easily using these simple steps:
- Crate a Packet Tracer Topology Lab
- Basic IP Setting for connectivity
- Set hostname and domain-name on Switch
- Set console and enable password for SSH login
- Generate the RSA Keys
- Setup the Line VTY configurations
- Create the username password for SSH access from PC
- Verify SSH access
For the configurations of SSH in packet tracer on Cisco switch, you are required to follow the above steps. Let start and perform these steps one by one. (Learn what is PSSH)
Crate a Packet Tracer Topology Lab
Our first step is to open the packet tracer and need to create a simple lab. For this topology we will use only one switch and a PC. Simply drag these two items on dashboard. Now we will connect them with straight through connection.
Basic IP Setting for connectivity
The next step is assign the suitable IP setting to these devices. For keeping it simple and making basic connectivity we will assign just two IP address to these device. We will assign the IP address to PC. For this will open the PC setting and then IP configuration. Here we will assign an IP address to host, in our case we are going to assign it 192.168.1.1 with the default gateway. For default gateway we will assign the IP address 192.168.1.10. We assign the second IP address to our Vlan1 interface on switch. And its IP address will be the gateway of host that is 192.168.1.10. For this we will use the basic commands.Switch> enable
Switch# config t
Switch(config)#interface vlan 1
Switch (config-if)# ip address 192.168.1.10 255.255.255.0
Switch (config -if)#no shut
Once you done with basic IP setting, you can verify the connectivity by pinging the interface vlan1 IP from host.
Set host-name and domain-name on Switch
For SSh configurations you need to configure a host-name and domain-name for your switch you can do this with these simple commands.
Switch # config t
Switch (config)#hostname SW1
SW1 ( config)#ip domain-name w7cloud.com
Set console and enable password for SSH login
For SSH access it is required that you must configure the console and enable password on your cisco switch. You can set these two passwords with following commands.
SW1 ( config)#line console 0
SW1(config-line)#password cisco
SW1(config -line)#logging synchronous
SW1(config- line)#login local
SW1 (config- line)#exit
Microsoft office 365 home premium product key generator windows 10. SW1 # enable secret cisco
Generate the RSA Keys
Your Cisco switch must have RSA keys that for the SSH process. You can generate the RSA keys with following command:
SW1 ( config)# crypto key generate rsa
How many bits in the modulus [512]: 1024
% Generating 1024 bit RSA keys, keys will be non-exportable…[OK]
Set the size of key to 1024 bits.
If your Cisco Switch is running an older version of Cisco IOS image, then it is extremely recommended that you upgrade to latest Cisco IOS.
Setup the Line VTY configurations
For the configuration of SSH on cisco switch you need the following line vty configurations, and input transport is required to set to SSH. Set the login-to-local, & password to 7.
sw1 ( config)#line vty 0 4
sw1 ( config-line)#transport input ssh
sw1( config -line)#login local
sw1(config- line)#password 7
sw1(config- line ) #exit
Create the username password for SSH access from PC
If you do not have a username for SSH access you need to create a username. You can do it with this simple command:
Sw1# config t
sw1 (config ) # username w7cloud password cisco
Make sure the password encryption services is enabled on your switch, this service will encrypt your password, & when you do “sh run”, you’ll see only the encrypted password, not clear text password.
SW1# service password-encryption
Verify SSH access from Host
Once you done with the above configurations you can test all these configuration by creating a SSH connection from Host. You do it the command ssh –l <username> <IP address>. Open the host command prompt and use the command
Free Keygens Downloads
C:>ssh -l waqas 192.168.1.10
Key Generator
It will ask for password, provide the password that you created with this username in previous steps. Then it asked for console password and then you need to provide the enable password. Now you are in your Cisco switch. You can perform switch configurations from your host.
From the switch, if you use the command ‘sh ip ssh’, it will also confirm that SSH is enabled on this cisco swith.
Crypto Key Generate Cisco 9904 Free
For better understanding please watch the video and like it.
I hope this will be a helpful for you, please share your comments. If you like this then share this on social media. Thank you for reading this.!
Guide on Cisco Router Configuration for Beginners
Free Key Generate Software
Related: 4 Best SSH Client Used by Professionals